Blockchain bridges are now a cornerstone of Web3 infrastructure, facilitating seamless transfer of assets and data between previously isolated blockchain networks. By linking diverse ecosystems, bridges foster true interoperability and empower users to leverage the unique strengths of multiple chains. Yet, this powerful functionality introduces substantial security risks, positioning bridges among the most vulnerable elements in the crypto landscape.
What Are Blockchain Bridges?
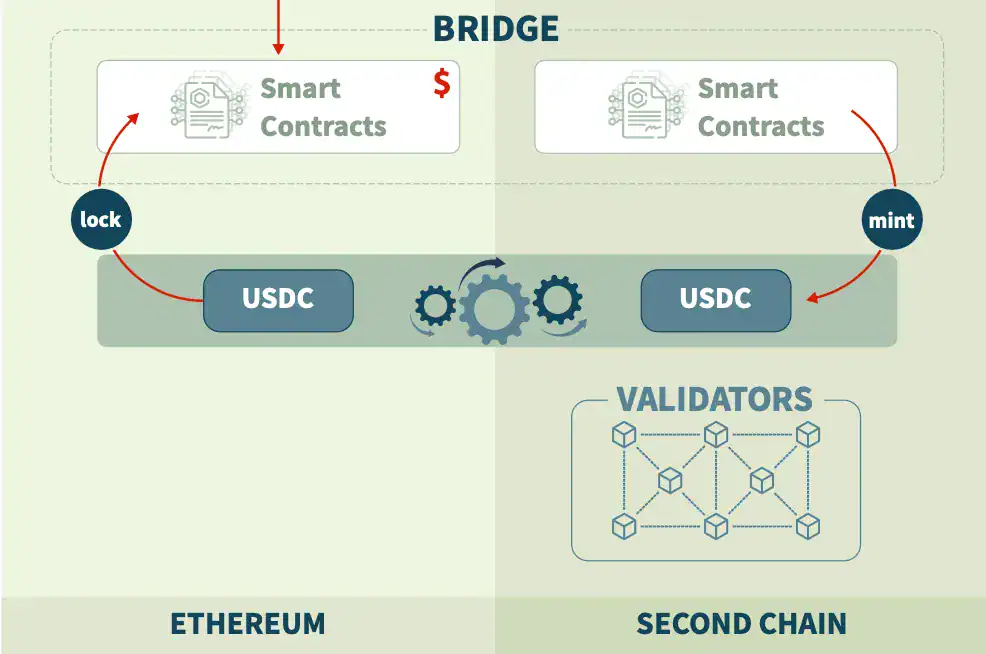
A blockchain bridge is a system that connects two or more blockchains, allowing them to communicate and transfer value. This can involve moving tokens, sharing data, or triggering smart contract actions across networks. Without bridges, each blockchain would remain siloed, limiting the overall potential of decentralized applications.
Bridges play a key role in enabling cross-chain interoperability, which is essential for scaling Web3. They allow users to access liquidity, lower fees, and different functionalities across multiple networks without needing to leave the ecosystem entirely.
Why Bridge Security Is a Major Concern
Despite their pivotal role, blockchain bridges are among the most actively targeted attack vectors in Web3. Their function as custodians of significant sums of locked assets during transfers makes them especially appealing to malicious actors.
Billions of dollars have already been lost to bridge exploits, underscoring the urgent need for robust security in cross-chain infrastructure.
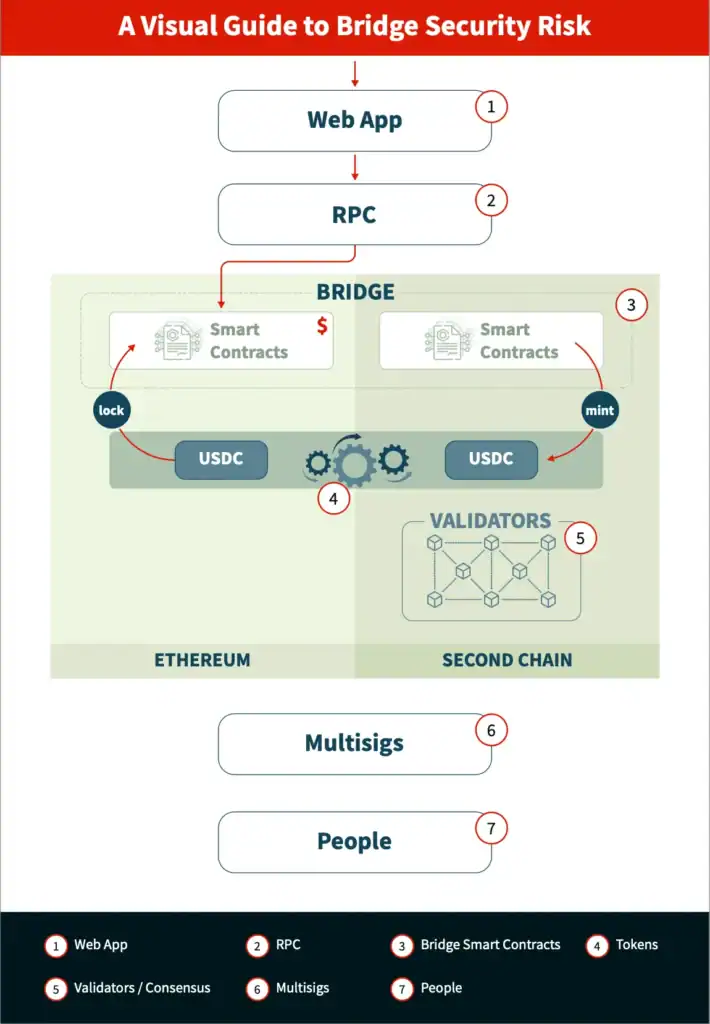
At the heart of the challenge is complexity. Bridges depend on a web of interrelated components—smart contracts, validators, off-chain systems, and communication protocols—each presenting its own vulnerabilities. This interconnectedness makes securing bridges far more difficult than securing single-chain applications.
Common Vulnerabilities in Blockchain Bridges
One of the most common risks is poor private key management. Many bridges depend on a set of validators or operators to approve transactions, and if these keys are compromised, attackers can gain control over the system.
Another major vulnerability is insufficient transaction monitoring. Without real-time detection systems, malicious activity can go unnoticed, allowing attackers to drain funds before any response is triggered.
Bridges are also exposed to smart contract bugs and logic errors. Since they often handle complex operations like locking, minting, and burning assets across chains, even small flaws in the code can lead to catastrophic losses.
Finally, the lack of rate limits and safeguards can amplify the damage of an attack. If there are no restrictions on how much value can be transferred in a short time, a successful exploit can result in the complete draining of a bridge’s funds.
Best Practices for Securing Blockchain Bridges
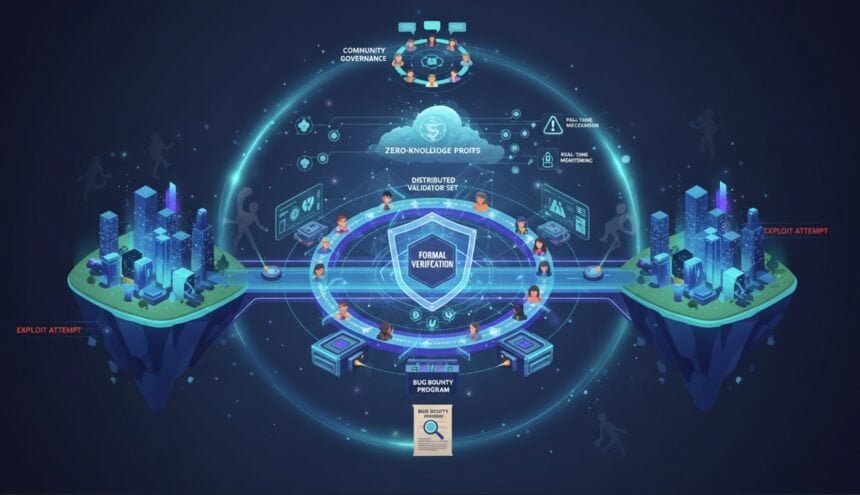
Securing a blockchain bridge demands a layered defense strategy, rather than reliance on a single protective measure. Rigorous private key management is fundamental, typically incorporating distributed validator sets and stringent operational security protocols.
Real-time monitoring systems should be implemented to detect abnormal activity and trigger emergency responses, such as pausing transactions. This can significantly reduce the impact of potential attacks.
Rate limits and withdrawal caps act as a final line of defense, ensuring that even if a vulnerability is exploited, the amount of value that can be extracted is limited.
Regular audits, bug bounty programs, and continuous testing are also crucial. Security should be treated as an ongoing process rather than a one-time checklist, as new vulnerabilities can emerge over time.
The Future of Bridge Security
As the blockchain ecosystem evolves into a multi-chain environment, bridges will remain essential infrastructure. However, their security must improve to keep pace with the value they secure.
Emerging approaches, such as decentralized validation systems and cryptographic proofs, aim to reduce trust assumptions and strengthen security guarantees. At the same time, better standards, tooling, and industry practices are helping developers build more resilient bridge architectures.
Final Words
Blockchain bridges will remain fundamental to the evolution of Web3, enabling interoperability and unlocking new opportunities across networks. However, their inherent complexity and the value they safeguard make them prime targets for increasingly sophisticated attacks.
To foster long-term growth and trust, developers and organizations must prioritize security—implementing layered defenses, continuous monitoring, and resilient infrastructure design. Without these proactive measures, the risks inherent to cross-chain systems will continue to impede the broader adoption of decentralized technologies.