The European Commission launched its age verification app on April 14, calling it a privacy-first tool built to the “highest standards.” Three days later, a security researcher cracked it open with a basic file edit on an Android phone.
Paul Moore, a UK-based security consultant, posted a screen recording on X showing the full bypass from start to finish. The whole thing took less than two minutes.
How the hack works
The app asks users to create a PIN during setup. It encrypts that PIN and saves it in the shared_prefs directory on the device. Moore identified two fundamental problems with this approach.
First, the PIN shouldn’t be stored locally at all. Second, and more critically, the encrypted PIN isn’t cryptographically tied to the vault that holds the user’s actual identity data. Those two things exist independently of each other.
That means an attacker with physical access to the device can delete the PinEnc and PinIV values from the shared_prefs file, restart the app and set a new PIN. When the app relaunches, it presents the original user’s credentials under the new PIN and treats them as valid.
It doesn’t stop there
Moore flagged additional flaws in the same configuration file. The app’s rate limiting, which is supposed to lock users out after too many failed PIN attempts, is just an incrementing number stored in the config. Reset it to zero and keep trying. Biometric authentication is controlled by a single boolean value called “UseBiometricAuth.” Set it to false and the app skips that step entirely.
Security experts on X questioned why the app doesn’t use the secure enclave hardware available on modern smartphones, relying instead on editable software-level files.
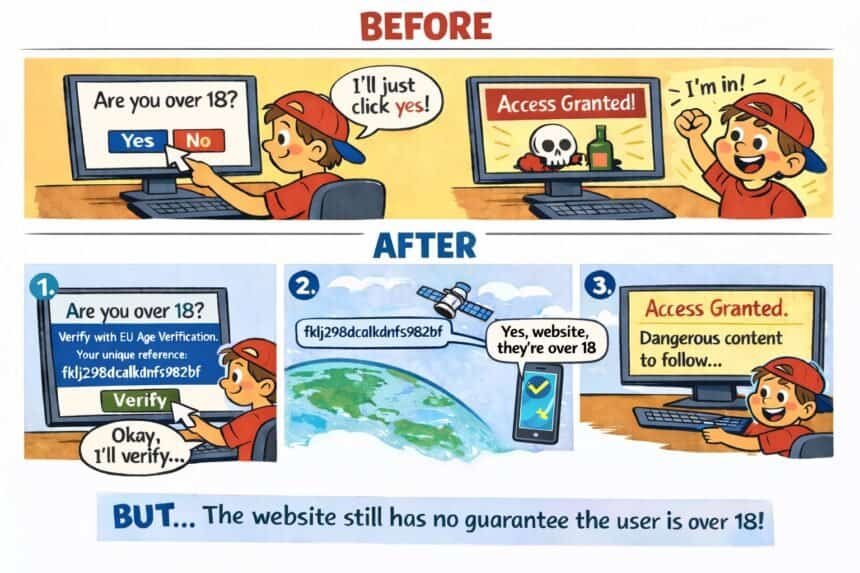
A prototype with real consequences
The app was built as a prototype for the broader European Digital Identity Wallet system. Six EU member states, including France, Spain and Denmark, are currently piloting it. Commission President Ursula von der Leyen praised it as “technically ready” and highlighted its open-source code as a transparency feature.
That transparency worked against the Commission. Moore’s video has racked up more than 2.6 million views. Over 405 security researchers had already signed an open letter warning that age verification laws reduce privacy and increase surveillance risks before the app even launched.
A separate architectural flaw discovered in March found that the app’s issuer component can’t verify whether passport validation occurred on the user’s device at all.
Moore addressed von der Leyen directly, warning that “this product will be the catalyst for an enormous breach at some point it’s just a matter of time.”
Telegram‘s Durov weighs in
Telegram founder Pavel Durov called the app “hackable by design,” arguing that its core mistake is blindly trusting the user’s device. He went further, suggesting the EU might use future breaches as justification to strip away the app’s privacy features and expand it into a broader surveillance tool.
The European Commission has not issued a patch or public response to the disclosed vulnerabilities as of April 18, 2026.